本網站使用cookies以改善您的使用體驗,並提供更優質的客製化內容。若您未改變cookies設定並繼續瀏覽我們的網站(點擊隱私權政策以獲得更多資訊),或點擊繼續瀏覽按鈕,代表您同意我們的隱私權政策及cookies的使用。
APP檢測
18.Aug.2020
行動應用程式蓬勃發展 你使用的APP真的安全嗎?
隨著科技及網路傳輸的發展,行動裝置應用日漸普及,許多APP應運而生,為人們帶來極高度的便利性,食衣住行育樂都能透過APP達成,儼然已成為生活中不可或缺的一環,也因此成為有心人士竊取資料的管道之一。相信大家在下載並使用APP時,經常會跳出要求授權手機的使用權限,像是通訊錄、撥打電話、麥克風及GPS定位等,大部分的使用者可能容易忽視APP在請求權限的相關性,讓惡意的APP取得不必要的系統權限,導致洩漏許多重要資訊。先前就曾有一款惡意的美顏相機APP,要求取得存取手機簡訊的權限,藉此取得發送至手機的簡訊認證碼,進一步啟動付費機制竊取使用者的金錢。除了上述APP要求不必要的系統權限外,APP還有其他常見的安全弱點,都會造成使用者資料外洩,以下將針對常見的APP弱點進行說明。
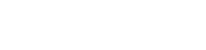
根據「開放網路軟體安全計畫」(Open Web Application Security Project,OWASP) 發表的常見行動裝置風險報告指出,絕大多數的APP存在多餘的功能模組、不安全的資料儲存及不安全的傳輸等安全問題,這些風險雖然不會有立即性的危害,但如今駭客的技術手法詭譎多變,一旦被找到實際未使用的模組並加以利用,不僅成為駭客下手的破口,造成資料外洩,抑或資料遭到惡意竄改,更嚴重還可能直接對企業內部系統造成不良的連鎖反應。舉例來說,「USB偵錯」(USB Debugging)是透過USB連接與Android SDK (Software Development Kit)進行溝通的一種方式,它允許使用者透過個人電腦控制Android設備與進行檔案傳輸等,並且能夠取得系統與APP的運作資訊,例如日誌檔案與設定檔等。過去也曾有惡意軟體透過USB感染Android裝置,「USB偵錯」可以說是雙面刃,在取得系統資訊的同時,也能讓行動裝置輕易地被控制,因此建議平常關閉該功能。
根據「開放網路軟體安全計畫」(Open Web Application Security Project,OWASP) 發表的常見行動裝置風險報告指出,絕大多數的APP存在多餘的功能模組、不安全的資料儲存及不安全的傳輸等安全問題,這些風險雖然不會有立即性的危害,但如今駭客的技術手法詭譎多變,一旦被找到實際未使用的模組並加以利用,不僅成為駭客下手的破口,造成資料外洩,抑或資料遭到惡意竄改,更嚴重還可能直接對企業內部系統造成不良的連鎖反應。舉例來說,「USB偵錯」(USB Debugging)是透過USB連接與Android SDK (Software Development Kit)進行溝通的一種方式,它允許使用者透過個人電腦控制Android設備與進行檔案傳輸等,並且能夠取得系統與APP的運作資訊,例如日誌檔案與設定檔等。過去也曾有惡意軟體透過USB感染Android裝置,「USB偵錯」可以說是雙面刃,在取得系統資訊的同時,也能讓行動裝置輕易地被控制,因此建議平常關閉該功能。
USB偵錯模式
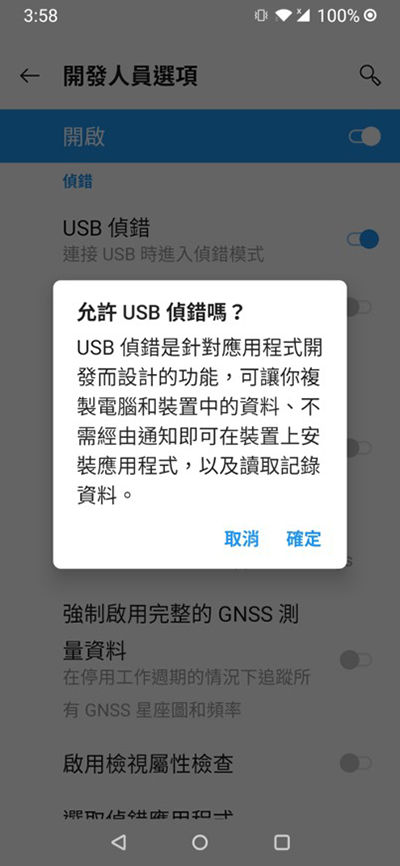
機敏資料的存儲或傳輸需進行加密
分析過去累積的APP檢測結果,開發者最容易疏忽的就是以明文形式儲存敏感資料。根據工業局的APP檢測基準,對於APP儲存在行動裝置上的內容,包括設定檔、資料庫檔、暫存檔及日誌檔等敏感資料,皆不得以明文形式儲存,須經過加密處理,以達到保護個人隱私的目的。因此,若APP在機敏資料的儲存或傳輸過程中未進行加密,或直接以明文形式存放在不安全的儲存位置,可能遭受其他任意且未經授權的APP進行存取,造成個人隱私的洩露。
以明文的形式儲存敏感資料
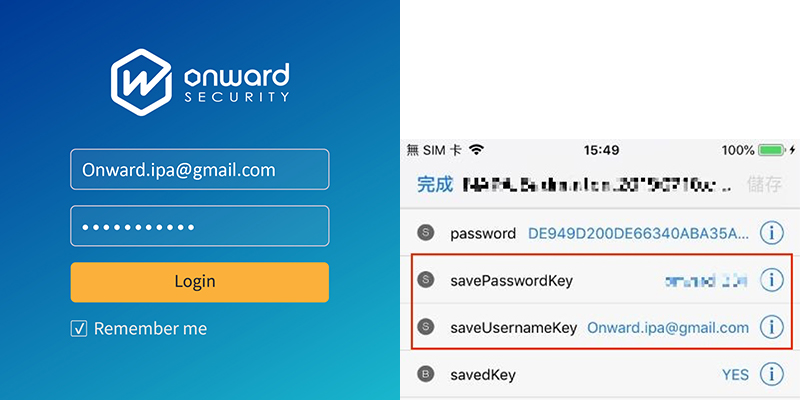
未正確檢查憑證可使重要資料外洩
絕大多數的APP都需透過網路連線與伺服器進行溝通,若疏於連線過程的資安防護,未檢查APP是否連線至正確的伺服器時,攻擊者便可利用中間人攻擊(Man-in-the-Middle Attack,MITM)方式竄改訊息、竊取資料及植入惡意程式。因此,開發人員必須注意在開發過程檢查憑證的正確性,若發現憑證過期或簽發單位資訊不正確時,必須立刻中斷連線,避免重要資料外洩。以下圖為例,當APP未檢查連線安全性時,攻擊者即可從中取得使用者登入帳號與密碼。
中間人攻擊示意圖;可攔截用戶敏感資訊
行動應用APP資安解決方案
針對企業所面臨的APP資安問題,安華聯網自2016年取得行動應用APP基本資安檢測基準合格實驗室後,已累積超過500個APP檢測經驗,客戶涵蓋政府、金融、電信、高科技、物聯網、航空及線上購物。此外,安華聯網同時能依循國際行動APP指引OWASP Mobile Security Testing Guide提供檢測服務,搭配原始碼掃描、弱點掃描、滲透測試、資安顧問及教育訓練等專業資安服務,提供廠商架構強化、資安檢測及顧問諮詢的一站式APP安全開發服務,全面提升雲端服務與APP安全性。

媒體報導
參考資料:
[1] TREND MICRO Security Intelligence Blog,< Fake Photo Beautification APPs on Google Play can Read SMS Verification Code to Trigger Wireless Application Protocol (WAP)/Carrier Billing>,2019.10.。
網址:https://blog.trendmicro.com/trendlabs-security-intelligence/fake-photo-beautification-APPs-on-google-play-can-read-sms-verification-code-to-trigger-wireless-APPlication-protocol-wap-carrier-billing/
[2] iThome,〈遺留無用功能或檔案而疏於防護〉,2019.04。
網址:https://www.ithome.com.tw/news/130259.
[3] 商業周刊,〈導入APP資安檢測〉,2019.07。閱於2020.06.29。
網址:https://www.businessweekly.com.tw/focus/indep/38870.
[4] 經濟部工業局,〈行動應用APP安全開發指引v1.2〉,2019.06。
[5] OWASP,“OWASP Mobile Top 10 2016”,2016.03。
網址:https://owasp.org/www-project-mobile-top-10