本網站使用cookies以改善您的使用體驗,並提供更優質的客製化內容。若您未改變cookies設定並繼續瀏覽我們的網站(點擊隱私權政策以獲得更多資訊),或點擊繼續瀏覽按鈕,代表您同意我們的隱私權政策及cookies的使用。
工控安全
19.Aug.2020
淺談智慧工廠的資安防禦實務(上)
錯誤的部署將招來資安危機
近年來政府極力推動工業4.0[1],又稱為智慧工廠(Smart Factory),重點在於產線的智慧化,需整合現有IT與OT技術,大量採用IoT設備,以因應快速變化的客製化製造需求,為了使生產流程最佳化,因此採用與部署大量的資安設備就成了必然的趨勢。然而再怎麼優良的資安產品,比如閘道防火牆,一但佈建錯誤便會失去防禦能力,進而成為資安的破口。多數駭客都偏好把目標設定在看起來「愚蠢」的目標,將目標打下,或納入殭屍網路(Botnet)轉為己用。而明顯的錯誤部署,勢必會讓駭客認為是「愚蠢」的目標,從而招來駭客的侵擾,導致全球製造業有21%的敏感資料外洩[2]。本文以實務角度作為切入點,淺談這巨大挑戰之中的防禦實務。
建置智慧工廠 得先瞭解合規建置架構
廠區內實務的建置架構,基於IEC 62443標準規範,美國國土安全部[3]建議有以下的配置,共可分成五到六層:
1. 場域裝置層 (Level-0: Field I/O Devices)
配置於生產線的感應器(Sensor)與執行器(Actuator),依照不同功能需求包含而不限於:繼電器、訊號與介面轉換器、控制閥、幫浦、馬達、風扇、燈號、輸送帶、機器手臂、切割機台、鑄模機台、自動化升降機與堆高機、廠區的監看CCTV等。2. 控制層 (Level-1: Basic Control and Safety Protection)
在標準規範下,這層也應當進行良好的安全防護。此層部署了眾多的遠距終端單元(RTU: Remote Terminal Unit)、人機介面(HMI: Human Machine Interface)、可程式化邏輯控制器(PLC: Programmable Logic Controller)[4],構作成分散式控制系統(Distributed Control Systems)的工業物聯網(Industrial IoT);而PLC作為關鍵設備,還包含眾多的功能性模組串連0級裝置的各種I/O進行程式化控制。3. 監督和區域流程控制層 (Level-2: Supervisory and Area Process Control)
將前兩層的種種數據,集結到監督控制與資料採集(SCADA: Supervisory Control and Data Acquisition)系統,能進行產線大數據蒐集、監控、分析,乃至於進行人工智慧運算、工廠自有雲端運算,打造智慧工廠內的數位神經網路。4. OT製造維運層 (Level-3: Site Manufacturing Operations and Control)
主要配置可整合多個SCADA系統資訊的維運工作站、長期日誌庫存機台。實務來說,前文的三個層級,都不應該擁有外網的連線能力,而由此層進行外網資源的擷取,並整合完外網的資源後,才散佈到需要使用外網資源的作業層與控制層。實務上,此層也會拆分出Level-3.5,配置『IT與OT之間』的非軍事區(DMZ),進行共用的資源存取,包含更新檔派送伺服器、內網校時伺服器,而大型的工廠場域,甚至需要在DMZ配置內部DNS,以便使用AD伺服器(Active Directory Services)進行資產登記與管理。而這層的DMZ,也不該任意對外網開放服務,通常IT僅會由跳板機(Jump Server)進行單向的OT遠端監控。5. 企業IT治理層 (Level-4: Enterprise IT Zone)
通常要建置構作與廠區網路實體隔離的企業商務區域,供給辦公室的共用檔案伺服器、企業資源管理(ERP、CRM、前述的AD伺服器)、印表機、內部郵件伺服器、極遠距不同辦公區進行內部網域串連的VPN伺服器,同時也可能會包含辦公室資安管理系統、SIEM等,支撐著企業商務業務、客戶服務、行政管理、產品研發設計、財務與稅務管理等等的OA營運單位日常運作。而美國國土安全部同樣建議將此層拆為兩層:現場業務規劃與物流網路層(Site Business Planning and Logistics Network)、企業IT治理層。在IT治理層之外,才有企業內網與網際網路間的非軍事區,配置用以提供包括企業之公眾瀏覽網站、檔案伺服器、網域伺服器、郵件伺服器等。![美國國土安全部[3]建議的工業4.0「安全網路架構」配置圖A](https://www.onwardsecurity.com/upload/news_resource_blog_b/ALL_news_resource_blog_22J18_pkjMvx7vg3.jpg)
美國國土安全部[3]建議的工業4.0「安全網路架構」配置圖A
![美國國土安全部[3]建議的工業4.0「安全網路架構」配置圖B](https://www.onwardsecurity.com/upload/news_resource_blog_b/ALL_news_resource_blog_22J18_NM1OHsrZTE.jpg)
美國國土安全部[3]建議的工業4.0「安全網路架構」配置圖B
![智慧製造工控分層範例:台灣電力公司的智慧電網資安設計[5]](https://www.onwardsecurity.com/upload/news_resource_blog_b/ALL_news_resource_blog_22J18_UDASNJxTFP.jpg)
智慧製造工控分層範例:台灣電力公司的智慧電網資安設計[5]
常見的錯誤部署
以下[6]部分內容會對照前文敘述的建置架構:
- 建置架構混亂與錯置,導致偵測與監控困難
- 將Level-0到Level-3的裝置,直接曝露在容易遭受攻擊的外網
- 曝露在外網的Level-3.5服務,沒有做好安全設定,或將設定修改成安全值
- 啟用或安裝不必要的功能
- 仍然使用工控產品預設的帳號密碼
- 對外顯示多餘資訊與程式偵錯資訊
- 安全防護功能被停用
- 升級的工控產品沒有做好安全設定
- 使用過期沒有再更新維護的工控產品
- 沒有啟用資產變更的偵測模組或相關資安產品
- 使用缺乏安全設定,不良的工控產品,而部署時無法符合建置架構
究竟駭客是怎麼入侵的?
在攻擊之前:偵查(Reconnaissance)
資安界的知名網站「Shodan.io」[7],是資安人員用來進行研究與監看全球連網設備基本訊息的付費搜尋引擎,至少能查到IPv4單點位於全球的哪個定點位置,對外開啟哪些連接埠口,接聽連接埠口的服務回應哪些明碼訊息,並且與Exploit-DB連結:可以查詢是否有相關的CVE弱點與該弱點的概念驗證程式;還能以國家、組織或ISP業者為單位,進行統計與產生報告。研究人員可依此向政府單位[8]報告網路使用狀況,或是企業組織查核自己管轄的IPv4在外網的狀態,或於商務來往時,進行資安查核。
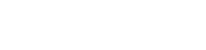
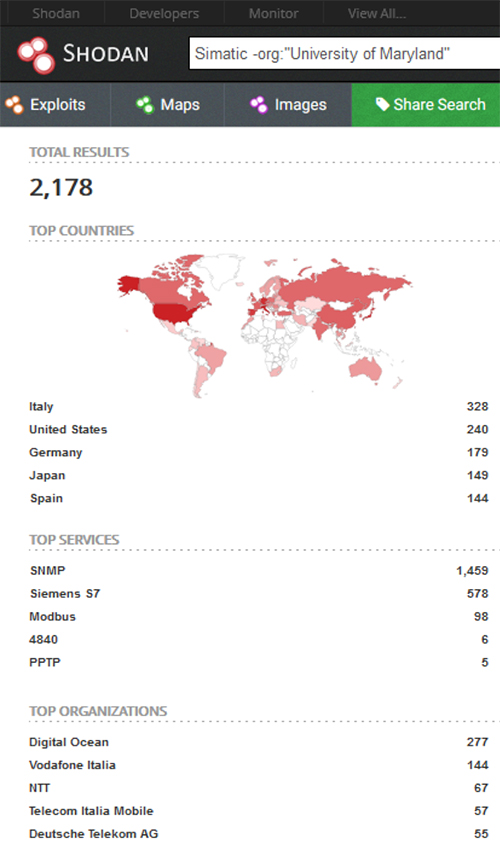
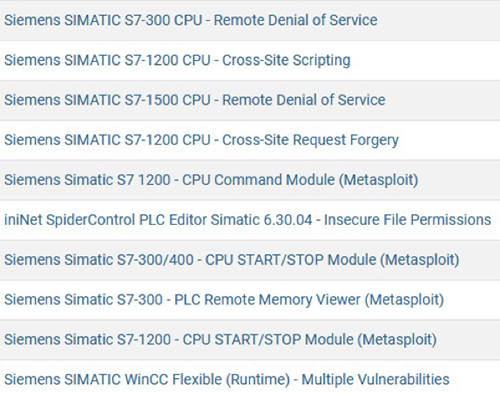
然而不單是研究人員,駭客同樣也會使用Shodan搜尋引擎來尋找攻擊目標。以西門子的工控產品為例[9][10],今年七月在Shodan上光是用關鍵字「Simatic」搜尋,全球就有2550筆連接埠口、含美國612筆、台灣13筆IPv4、日本149筆、中國67筆,明碼標示含有西門子工控產品名稱的連接埠口。進一步分析全球資料的組成,其中包含美國馬里蘭州大學研究駭客攻擊行為的HoneyPots共372筆;扣除所有美國馬里蘭州大學的資料後,而僅應該部署在內網,卻真實曝露在網路上的西門子SNMP服務有1459筆資料、西門子PLC模組型號S7有578筆、連結SCADA與RTU的西門子Modbus有98筆資料。其中甚至不乏有HTTP埠口,可以進入到PLC模組或路由閘道的Web登入畫面,假設部署人員未更改預設的帳號密碼,或是駭客進行Brute Force破解帳號密碼,就可能得以控制該PLC模組或閘道。作為研究人員,實際上Shodan查詢時,也直接看到某些SIMATIC模組[12],可以無密碼直接訪問,進行像是查看內網資訊、檢視HMI資訊等。
Shodan.io查詢畫面一隅
![查到可以無密碼進入存取的西門子SIMATIC PLC模組[12]](https://www.onwardsecurity.com/upload/news_resource_blog_b/ALL_news_resource_blog_22J18_hWjounKCY3.jpg)
查到可以無密碼進入存取的西門子SIMATIC PLC模組[12]
Exploit-DB一隅:西門子工控產品的概念驗證程式
上述僅僅是以西門子的工控產品為例,Shodan上還能查到更多其他工控產品、IT產品與物聯網產品的資訊,包含的CVE弱點項目更是五花八門。況且Exploit-DB的概念驗證程式僅是冰山一角:而隱藏於暗網,駭客們互相交易的地下市集,則充斥更多的攻擊與控制型惡意程式。
参考資料:
[1]《WHITE PAPER : Smarter Security for Manufacturing in The Industry 4.0 Era - Industry 4.0 Cyber Resilience for the Manufacturing of the Future》Broadcom、Symantec. URL:https://docs.broadcom.com/doc/industry-4.0-en
[2]《2019 GLOBAL DATA RISK REPORT FROM THE VARONIS DATA LAB》Varonis。URL:https://info.varonis.com/hubfs/Varonis%202019%20Global%20Data%20Risk%20Report.pdf#page=20
[3]《Recommended Practice: Improving Industrial Control System Cybersecurity with Defense-in-Depth Strategies》Industrial Control Systems Cyber Emergency Response Team, CISA, Department of Homeland Security. URL:https://us-cert.cisa.gov/sites/default/files/recommended_practices/NCCIC_ICS-CERT_Defense_in_Depth_2016_S508C.pdf
[4]《Programmable Logic Controllers - Security Threats and Solutions》Texas Instruments. https://www.ti.com/lit/an/spraco8/spraco8.pdf
[5]《Smart Grid: Security》. URL:https://smartgrid.taipower.com.tw/en/page.aspx?mid=15
[6]《OWASP Top Ten》OWASP. URL:https://owasp.org/www-project-top-ten/
[7]《Shodan Help Center: Navigating the Website》Shodan.io. URL:https://help.shodan.io/the-basics/navigating-the-website
[8]《US government warns over vulnerable control systems》BBC UK. URL:https://www.bbc.com/news/technology-20984827
[9]《CVE Details: Siemens Products》CVE Details. URL:https://www.cvedetails.com/product-list/product_type-/vendor_id-109/firstchar-S/page-3/products.html
[10]《工業控制系統安全之探討-以西門子S7系列為例》陸冠竹、劉奕賢、劉宗晁、李忠憲。國立成功大學電機工程學系 / 電腦與通信工程研究所。2019 臺灣網際網路研討會線上論文集. URL:https://tanet2019.nsysu.edu.tw/thesises.php
[11]《MITRE ATT&CK MATRIX》MITRE. URL:https://attack.mitre.org/
[12]《SIEMENS SIMATIC NET: S7-CPs for Industrial Ethernet -- CP 343-1 / CP 343-1 EX20》SIEMENS公司. URL:https://cache.industry.siemens.com/dl/files/308/8777308/att_39695/v1/ghb3431_e.pdf
補充資料:
[1]《SIEMENS SIMATIC S7-300: S7-300 Module data - Manual》SIEMENS. URL:https://cache.industry.siemens.com/dl/files/629/8859629/att_55794/v1/s7300_module_data_manual_en-US_en-US.pdf
[2]《SIEMENS SIMATIC S7: S7-1200 Programmable controller - System Manual》SIEMENS. URL:https://cache.industry.siemens.com/dl/files/465/36932465/att_106119/v1/s71200_system_manual_en-US_en-US.pdf
然而不單是研究人員,駭客同樣也會使用Shodan搜尋引擎來尋找攻擊目標。以西門子的工控產品為例[9][10],今年七月在Shodan上光是用關鍵字「Simatic」搜尋,全球就有2550筆連接埠口、含美國612筆、台灣13筆IPv4、日本149筆、中國67筆,明碼標示含有西門子工控產品名稱的連接埠口。進一步分析全球資料的組成,其中包含美國馬里蘭州大學研究駭客攻擊行為的HoneyPots共372筆;扣除所有美國馬里蘭州大學的資料後,而僅應該部署在內網,卻真實曝露在網路上的西門子SNMP服務有1459筆資料、西門子PLC模組型號S7有578筆、連結SCADA與RTU的西門子Modbus有98筆資料。其中甚至不乏有HTTP埠口,可以進入到PLC模組或路由閘道的Web登入畫面,假設部署人員未更改預設的帳號密碼,或是駭客進行Brute Force破解帳號密碼,就可能得以控制該PLC模組或閘道。作為研究人員,實際上Shodan查詢時,也直接看到某些SIMATIC模組[12],可以無密碼直接訪問,進行像是查看內網資訊、檢視HMI資訊等。
Shodan.io查詢畫面一隅
![查到可以無密碼進入存取的西門子SIMATIC PLC模組[12]](https://www.onwardsecurity.com/upload/news_resource_blog_b/ALL_news_resource_blog_22J18_hWjounKCY3.jpg)
查到可以無密碼進入存取的西門子SIMATIC PLC模組[12]
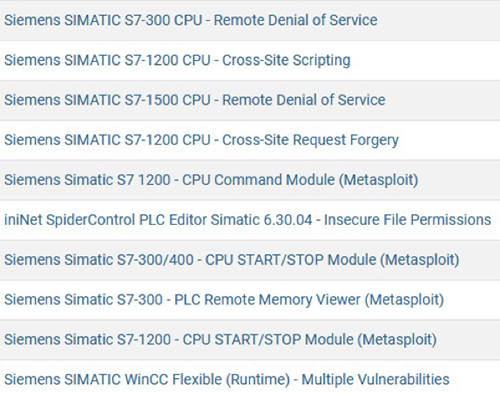
Exploit-DB一隅:西門子工控產品的概念驗證程式
上述僅僅是以西門子的工控產品為例,Shodan上還能查到更多其他工控產品、IT產品與物聯網產品的資訊,包含的CVE弱點項目更是五花八門。況且Exploit-DB的概念驗證程式僅是冰山一角:而隱藏於暗網,駭客們互相交易的地下市集,則充斥更多的攻擊與控制型惡意程式。
錯誤部署讓駭客得以直接進行攻擊
根據MITRE ATT&CK矩陣[11],假設偵查到曝露於外網的西門子SNMP服務、S7型號PLC模組,含有CVE漏洞或其他未知的漏洞被攻擊,就屬於矩陣上「外部遠端服務」(External Remote Services)的範疇,甚至可能得以透過曝露在外網的UDP埠口161、162或TCP埠口102,進行DoS / DDoS攻擊以阻斷服務,阻斷服務將有可能造成產線監控失效、產線停擺、或產線失控。
假設PLC模組或路由閘道的Web登入畫面含有弱點、或帳號密碼被取得,就可能實現矩陣上「開採對外應用」(Exploit Public-Facing Application)的範疇。如果被駭客取得完整控制權,駭客將可利用作為殭屍網路與攻擊跳板,或是長期潛伏(APT),偷竊廠區的商業機密。
假設PLC模組或路由閘道的Web登入畫面含有弱點、或帳號密碼被取得,就可能實現矩陣上「開採對外應用」(Exploit Public-Facing Application)的範疇。如果被駭客取得完整控制權,駭客將可利用作為殭屍網路與攻擊跳板,或是長期潛伏(APT),偷竊廠區的商業機密。
智慧製造維運管理的第一道防線:安全部署(Security Deployment)
接下來我們以DevSecOps的PDCA循環來談,其中所謂的安全部署,包含檢查安裝(Signature Verify、Integrity Checks)、進行安全設定(Security Configuration)、啟用安全稽核(Security Audit)。在進行安全設定的過程,細項可說是多如牛毛。OWASP TOP 10[6]列出的網站10大資安風險,在一定程度上,也同樣適用於工控環境。根據統計,其中第6大風險,即為「錯誤的安全設定」(Security Misconfiguration)。
在部署完成後,才是日常的維運:監控、偵測、分析事件、控制事件影響範圍、事件回應與報告、維持維運穩定。換句話說,部署是否良好,會直接影響維運的安全性與穩定性。
在部署完成後,才是日常的維運:監控、偵測、分析事件、控制事件影響範圍、事件回應與報告、維持維運穩定。換句話說,部署是否良好,會直接影響維運的安全性與穩定性。
防禦實務:修正導致錯誤部署的原因 且重新進行安全部署
綜合來說,會導致錯誤部署,從而導致PDCA循環斷鍊,至少包括而不限於以下原因與建議解決辦法,依照PCDA分類排序:
原因1: 不良的部署計畫(Plan)
- 建置前沒有完整的部署計畫,導致建置架構錯亂
- 由於缺乏部署計畫,導致內網與外網沒有區隔或區隔薄弱
- 部署項目多如牛毛,部署人員一時大意,導致應列入的部署項目卻未列入部署查核清單
- 開發商或開發人員沒有完整交接,給予部署人員產品安全設定的規格內容
- 開發商或開發人員製作的部署文件與使用者手冊包含錯誤部署設定
- 未有部署後維運監控計畫,導致沒有安全稽核設定
建議解決辦法: 尋求專業資安架構師,協助進行
- 完整部署規劃
- 完整部署查核清單規劃
- 完整維運監控規劃
原因2: 部署人員能力與人力不足(Do)
- 部署人員對於工控資安標準不夠清楚
- 部署人員僅知道硬體裝設,不知需要軟韌體設定
- 部署人員是未受訓的臨時工
- 部署人員受訓後仍未熟悉
- 部署工作量太大,時間有限卻人力不足,導致草草交差
- 部署人員對於啟用軟體稽核不夠清楚
- 兼任的內部稽核人員,僅知道硬體設備的交接項目
- 部署人員未依照工控產品的使用手冊進行部署
建議解決辦法: 尋求資安專家,協助進行教育訓練
- 加強部署人員的專業資安教育訓練
- 加強稽核人員的專業資安教育訓練
原因3: 部署過程缺乏內部稽核(Check)
- 機構未設有專任內部資安人員與稽核人員
- 工控產品設計不良,無法在部署前檢查封裝
- 部署人員過度依賴設定不良的自動化部署工具
- 部署的工控產品具有開發不良的釋出版本
- 部署的工控產品包含漏洞而未加確認並予以保護
- 部署的工控產品缺乏軟體稽核設計,無法開啟稽核功能
建議解決辦法
- 依照法規,設置專職資安稽核人員
- 要求工控產品開發商,提供第三方檢測的產品資安檢測報告
- 採購可稽核的工控與監控設備,並啟用稽核功能
原因4: 企業文化の問題(Act)
- 客戶或企業高層缺乏維運管理與資安相關知識,輕忽資安的重要性,導致沒有資安承諾與部署計畫
- 部署時或部署後,被客戶或企業高層要求「方便企業交流卻缺乏資訊安全」的錯誤配置
- 企業內部缺乏資安教育訓練
- 企業主給予維運與部署人員過低的薪酬、過高的工時、過量的工作負荷、惡質的情緒對待、非人道的人身安全對待、或工廠所製造的產品其本質的社會價值不受員工認同,從而導致人員缺乏工作熱誠與職業倦怠,產生不良的部署與監控品質,甚至員工產生報復心態,成為駭客
建議解決辦法: 尋求資安專家、企業管理專家或企業倫理專家,協助進行
- 整體企業的基礎資安教育訓練
- 改善整體企業文化,以獎勵代替懲罰,提高員工向心力與工作執行力
安華聯網的智慧工廠資安服務與自主研發產品
安華聯網具備智慧工廠資安服務與自主研發產品解決方案,主要提供IEC 62443、ISO 27001等資安合規與認驗證服務,協助廠商進行安全部署計劃與稽核,能快速取得國際標準證書,以提升客戶的信賴及企業商譽。而工控產品或系統的資安檢測服務,可滿足軟硬體之資安要求,適用於行動裝置、智慧家電、智能汽車、網通、安控等物聯網產品,以及PLC、ICS、SCADA等智慧製造相關之工控元件。
同時提供軟體安全開發指導服務,協助廠商具備軟體安全開發能量,進行專業的軟體開發安全教育訓練、維運資訊安全管理教育訓練,幫助技術人員建立與工業物聯網相關的資安意識,以因應未來智慧製造的建置以及工業4.0時代的來臨。
自主研發的產品資安管理系統「HERCULES SecFlow」,提供全方位的產品安全開發管理系統化解決方案,符合DevSecOps,從需求、設計、開發、測試到部署階段,提供產品安全流程管理、產品韌體安全檢測、主動式產品安全事件監控與通報等,協助客戶快速建立安全的軟體開發流程,並支援 ISO 27001、ISO 27034、OpenSAMM、NIST SP 800-64 等合規標準。此外,也持續自主研發未來次世代的進階版本,滿足部署前後的維運監控需求,包含多元的端點資產監控、風險評估、多標準的資安政策管理等進階功能,並適用於MITRE ATT&CK資安防護框架。
另一項產品弱點檢測自動化工具「HERCULES SecDevice」,是針對連網產品所設計的自動化安全評估工具,具備已知弱點測試、模糊測試與網頁安全測試等功能,並採用專利AI學習技術,加速檢測時間,提升弱點檢測之正確性。測試評估的範圍涵蓋IEC 62443、OWASP TOP 10 與 CWE/SANS TOP 25 等安全要求。
淺談智慧工廠的資安防禦實務 下篇文章:淺談智慧工廠的資安防禦實務(下)
媒體報導
同時提供軟體安全開發指導服務,協助廠商具備軟體安全開發能量,進行專業的軟體開發安全教育訓練、維運資訊安全管理教育訓練,幫助技術人員建立與工業物聯網相關的資安意識,以因應未來智慧製造的建置以及工業4.0時代的來臨。
自主研發的產品資安管理系統「HERCULES SecFlow」,提供全方位的產品安全開發管理系統化解決方案,符合DevSecOps,從需求、設計、開發、測試到部署階段,提供產品安全流程管理、產品韌體安全檢測、主動式產品安全事件監控與通報等,協助客戶快速建立安全的軟體開發流程,並支援 ISO 27001、ISO 27034、OpenSAMM、NIST SP 800-64 等合規標準。此外,也持續自主研發未來次世代的進階版本,滿足部署前後的維運監控需求,包含多元的端點資產監控、風險評估、多標準的資安政策管理等進階功能,並適用於MITRE ATT&CK資安防護框架。
另一項產品弱點檢測自動化工具「HERCULES SecDevice」,是針對連網產品所設計的自動化安全評估工具,具備已知弱點測試、模糊測試與網頁安全測試等功能,並採用專利AI學習技術,加速檢測時間,提升弱點檢測之正確性。測試評估的範圍涵蓋IEC 62443、OWASP TOP 10 與 CWE/SANS TOP 25 等安全要求。
淺談智慧工廠的資安防禦實務 下篇文章:淺談智慧工廠的資安防禦實務(下)
媒體報導
参考資料:
[1]《WHITE PAPER : Smarter Security for Manufacturing in The Industry 4.0 Era - Industry 4.0 Cyber Resilience for the Manufacturing of the Future》Broadcom、Symantec. URL:https://docs.broadcom.com/doc/industry-4.0-en
[2]《2019 GLOBAL DATA RISK REPORT FROM THE VARONIS DATA LAB》Varonis。URL:https://info.varonis.com/hubfs/Varonis%202019%20Global%20Data%20Risk%20Report.pdf#page=20
[3]《Recommended Practice: Improving Industrial Control System Cybersecurity with Defense-in-Depth Strategies》Industrial Control Systems Cyber Emergency Response Team, CISA, Department of Homeland Security. URL:https://us-cert.cisa.gov/sites/default/files/recommended_practices/NCCIC_ICS-CERT_Defense_in_Depth_2016_S508C.pdf
[4]《Programmable Logic Controllers - Security Threats and Solutions》Texas Instruments. https://www.ti.com/lit/an/spraco8/spraco8.pdf
[5]《Smart Grid: Security》. URL:https://smartgrid.taipower.com.tw/en/page.aspx?mid=15
[6]《OWASP Top Ten》OWASP. URL:https://owasp.org/www-project-top-ten/
[7]《Shodan Help Center: Navigating the Website》Shodan.io. URL:https://help.shodan.io/the-basics/navigating-the-website
[8]《US government warns over vulnerable control systems》BBC UK. URL:https://www.bbc.com/news/technology-20984827
[9]《CVE Details: Siemens Products》CVE Details. URL:https://www.cvedetails.com/product-list/product_type-/vendor_id-109/firstchar-S/page-3/products.html
[10]《工業控制系統安全之探討-以西門子S7系列為例》陸冠竹、劉奕賢、劉宗晁、李忠憲。國立成功大學電機工程學系 / 電腦與通信工程研究所。2019 臺灣網際網路研討會線上論文集. URL:https://tanet2019.nsysu.edu.tw/thesises.php
[11]《MITRE ATT&CK MATRIX》MITRE. URL:https://attack.mitre.org/
[12]《SIEMENS SIMATIC NET: S7-CPs for Industrial Ethernet -- CP 343-1 / CP 343-1 EX20》SIEMENS公司. URL:https://cache.industry.siemens.com/dl/files/308/8777308/att_39695/v1/ghb3431_e.pdf
補充資料:
[1]《SIEMENS SIMATIC S7-300: S7-300 Module data - Manual》SIEMENS. URL:https://cache.industry.siemens.com/dl/files/629/8859629/att_55794/v1/s7300_module_data_manual_en-US_en-US.pdf
[2]《SIEMENS SIMATIC S7: S7-1200 Programmable controller - System Manual》SIEMENS. URL:https://cache.industry.siemens.com/dl/files/465/36932465/att_106119/v1/s71200_system_manual_en-US_en-US.pdf