本網站使用cookies以改善您的使用體驗,並提供更優質的客製化內容。若您未改變cookies設定並繼續瀏覽我們的網站(點擊隱私權政策以獲得更多資訊),或點擊繼續瀏覽按鈕,代表您同意我們的隱私權政策及cookies的使用。
工控安全
12.Oct.2020
工控安全標準與實際運用-淺談IEC62443
2015 年 12 月 23 日烏克蘭電力網路受到駭客攻擊,導致伊萬諾-弗蘭科夫斯克州大停電,這個世界第一起駭客攻擊造成電網大規模的停電事件,使關鍵基礎設施的資安威脅受到各方高度重視,而台灣從2018年的半導體業機臺中毒事件後,陸續發生了製造業、工業領域以及醫療產業的資安事件,而這些只是大規模複雜攻擊行動的一部分,上述這些網路罪犯攻擊重要基礎設施系統的案例,讓許多資安廠商紛紛針對重大民生基礎設施的資安風險與因應策略投入研究,而OT的資安也越來越受重視,也因此國際電工組織委員會自2013年開始陸續發布了IEC 62443的系列標準,而以製造業起家的台灣,自然而然也被歐美大廠要求需符合IEC 62443系列工控標準取得證書,以減少工控資安的風險。
針對工控物聯網的安全,您瞭解多少?
工業控制系統因應物聯網發展,包含越來越多的自動化控制系統、電腦運算與伺服器服務,這些網路互聯的普及與融合造成OT環境系統安全受到威脅,再加上近來不斷升溫政治衝突、恐怖主義與經濟犯罪,都是引發多面向攻擊產業關鍵基礎設施的動機,也因此,國際電工組織委員會針對工控安全特別參照ISA 99制定IEC 62443,稍後ISA 99也將標準更名為ISA/IEC 62443。ISA/IEC 62443有不同系列標準,除了能讓各個工控領域的上、中、下游廠商能有各自對應的標準外,未來在標準更新時,拿證單位也只需要針對適用於該更新標準的單位,依需求再決定是否需要標準更新的證書,而不需要一體適用於全部廠商,對廠商而言可以分散資安風險、減少導入資安標準的成本與人力,同時也可以在發生資安事件時,快速找出原因,並進行適當的處理措施。
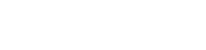
圖一 IEC/PAS 62443-3 Security life cycle
產品的資安生命週期可從人機介面、實體環境及電子邏輯介面三個角度來看,從設計、佈署、維運、監測、管理、緊急事件處理與維運,每一個階段環環相扣,在IEC/PAS 62443-3標準對於工控安全的生命週期更為重視,可由圖一中得知在每個階段都有相對應要注意的事項,其目的是為了減少資安風險與威脅,以維護整個產品生命週期的資訊安全。
而工控系統常見的威脅可來自公共破壞者或恐怖份子,被攻擊後的工控系統會因為失效而造成資安事故、阻絕攻擊、機密性漏洞(例如生產資訊的揭露)、法律漏洞、天災(例如非預期的天災)或是其它組織內特殊的考量因素,皆會依其影響產品功能的嚴重性來決定呈報的管理層級、呈報速度、相關的因應措施以及應涉及的主管層級。為了避免這些威脅的發生,風險評估在工控安全的活動中,是不可或缺的一環;而降低風險的措施可透過金錢的投資、技術的運用、實體的保護設計以及組織管理等方式,來共同保護資產的價值。
工控安全要考量的面向需俱備廣泛性,因此IEC 62443的標準參考了ISO/IEC 15408 共通準則 (實體安全、產品開發生命週期等)、ISO/IEC 27002 資訊安全最佳實例、ISO/IEC 27001 資訊安全管理系統、ISO/IEC Guide 73:2002 風險評估、NIST 800-53 風險控制措施以及ISO 19790 密碼模組等標準,就是希望能從各種不同的角度以及不同的曝險程度來訂定相對應的工控安全規範。
與一般的ISO/IEC標準不同的是,若想取得IEC 62443-4-2與IEC 62443-3-3的證書,必須先通過IEC 62443 -4-1的認證,也就是說對產品供應商而言,必須先確保機構內的產品開發流程安全後,才能申請產品安全認證。目前有愈來愈多IoT設備面對國外市場已陸續被要求提供設備安全等級(Security Level)證明,而IEC 62443 -4-2規範的便是對於安全等級(Security Level)的要求細節,因此隨著市場對安全需求的增加,IEC62443-4-2認證也日顯重要。
驗證IEC 62443-4-2首先須依據IEC 62443-4-1定義的開發流程來實作IEC 62443-4-2的組件,組件涵蓋軟體應用(Software Application)、嵌入式設備(Embedded device)、網通設備(Network device)以及控制設備(Host device)四類;再來技術安全也需滿足自訂安全等級(Security Level)目標下的所有要求項目,才能順利取得證書。
然而對已經有開發能力的機構而言,本身就已具備既有的產品開發流程,又該如何調整才能達到IEC 62443-4-1對於產品安全開發的要求?
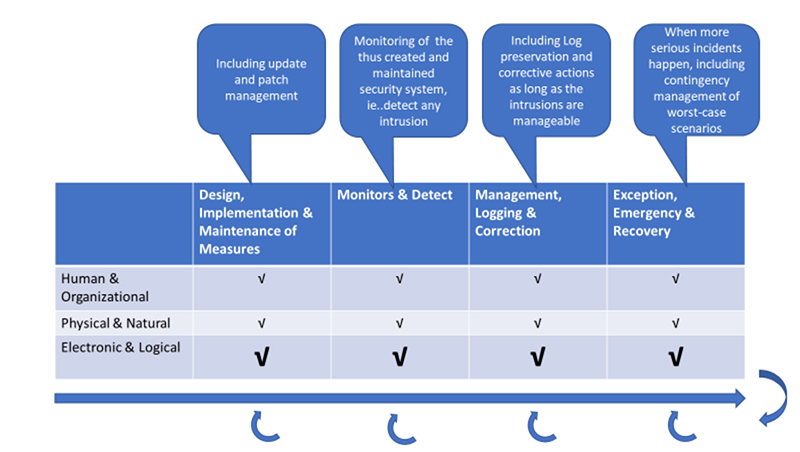
圖二:角色與標準流程對應圖
從各角色與標準對應流程關係中(參考圖二:角色與標準流程對應圖),可以歸納出開發環境兩項執行重點,一是安全開發的框架:含括了安全的設計、縱深防禦的概念以及如何管理產品生命週期,包含建立、維護以及產品失效的流程;二是在開發流程中,必須將產品開發的流程包含安全組態、更新管理政策以及其他相關的安全開發流程妥善的記錄並留存,同時也必須執行安全測試以達到IEC 62443-4-1的安全開發流程要求。
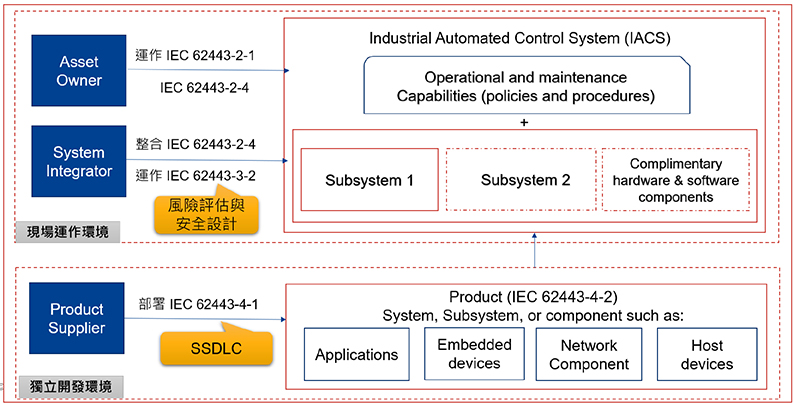
圖三:成熟等級(Maturity Level)與安全級別(Security Level)
参考資料:
[1] IEC/PAS 62443-3 Publicly available specification Pre-Standard
[2] IEC/PAS 62443-4-1 Secure Product Development Lifecycle Requirements
工控產品生命週期與威脅!
資訊安全本質被視為是永遠沒有停止線的生命週期(除非產品被宣稱為End of license),在產品的生命週期需要持續性、定期採取工控系統(ICS, Industrial control system)安全措施以防止受到多面向的資安威脅。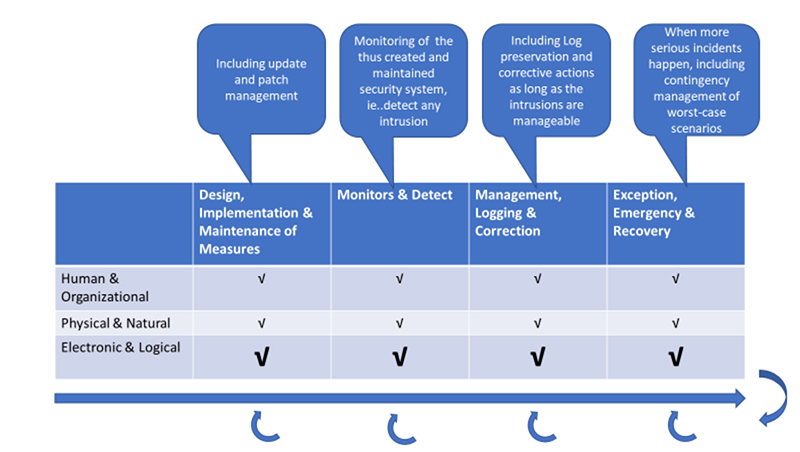
圖一 IEC/PAS 62443-3 Security life cycle
產品的資安生命週期可從人機介面、實體環境及電子邏輯介面三個角度來看,從設計、佈署、維運、監測、管理、緊急事件處理與維運,每一個階段環環相扣,在IEC/PAS 62443-3標準對於工控安全的生命週期更為重視,可由圖一中得知在每個階段都有相對應要注意的事項,其目的是為了減少資安風險與威脅,以維護整個產品生命週期的資訊安全。
而工控系統常見的威脅可來自公共破壞者或恐怖份子,被攻擊後的工控系統會因為失效而造成資安事故、阻絕攻擊、機密性漏洞(例如生產資訊的揭露)、法律漏洞、天災(例如非預期的天災)或是其它組織內特殊的考量因素,皆會依其影響產品功能的嚴重性來決定呈報的管理層級、呈報速度、相關的因應措施以及應涉及的主管層級。為了避免這些威脅的發生,風險評估在工控安全的活動中,是不可或缺的一環;而降低風險的措施可透過金錢的投資、技術的運用、實體的保護設計以及組織管理等方式,來共同保護資產的價值。
工控安全要考量的面向需俱備廣泛性,因此IEC 62443的標準參考了ISO/IEC 15408 共通準則 (實體安全、產品開發生命週期等)、ISO/IEC 27002 資訊安全最佳實例、ISO/IEC 27001 資訊安全管理系統、ISO/IEC Guide 73:2002 風險評估、NIST 800-53 風險控制措施以及ISO 19790 密碼模組等標準,就是希望能從各種不同的角度以及不同的曝險程度來訂定相對應的工控安全規範。
IEC 62443認驗證知多少!
IEC62443可以認證的標準包含程序流程及產品安全兩個類別,如下表所示:| 認證類別 | 系列標準 | 適用對象 |
|---|---|---|
| 程序流程 | 62443-2-4 IACS的服務供應商安全計劃要求 (Security program requirements for IACS service providers) | 系統整合商 |
| 62443-4-1 安全產品開發生命週期要求 (Secure product development lifecycle requirements) | 產品供應商 | |
| 產品安全 | 62443-3-3 系統安全要求與安全等級 (System Security requirements and security levels) | 系統整合商 |
| 62443-4-2 IACS元件的技術安全要求 (Technical Security requirements for IACS components) | 產品供應商 |
表一:認證類別與系統標準
與一般的ISO/IEC標準不同的是,若想取得IEC 62443-4-2與IEC 62443-3-3的證書,必須先通過IEC 62443 -4-1的認證,也就是說對產品供應商而言,必須先確保機構內的產品開發流程安全後,才能申請產品安全認證。目前有愈來愈多IoT設備面對國外市場已陸續被要求提供設備安全等級(Security Level)證明,而IEC 62443 -4-2規範的便是對於安全等級(Security Level)的要求細節,因此隨著市場對安全需求的增加,IEC62443-4-2認證也日顯重要。
驗證IEC 62443-4-2首先須依據IEC 62443-4-1定義的開發流程來實作IEC 62443-4-2的組件,組件涵蓋軟體應用(Software Application)、嵌入式設備(Embedded device)、網通設備(Network device)以及控制設備(Host device)四類;再來技術安全也需滿足自訂安全等級(Security Level)目標下的所有要求項目,才能順利取得證書。
然而對已經有開發能力的機構而言,本身就已具備既有的產品開發流程,又該如何調整才能達到IEC 62443-4-1對於產品安全開發的要求?
認證最重要的基礎-產品安全開發流程
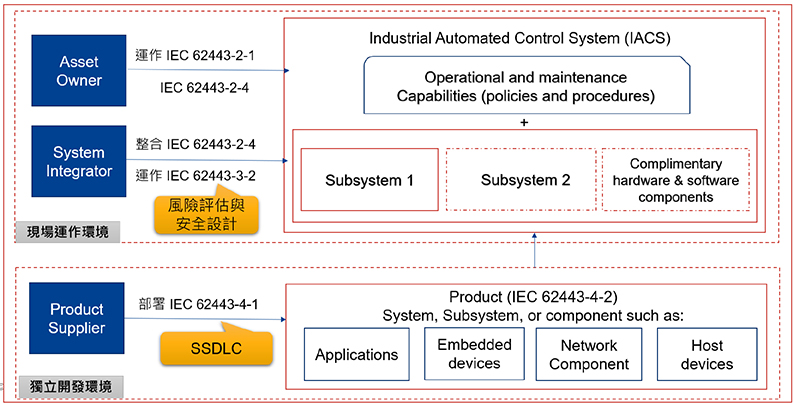
圖二:角色與標準流程對應圖
從各角色與標準對應流程關係中(參考圖二:角色與標準流程對應圖),可以歸納出開發環境兩項執行重點,一是安全開發的框架:含括了安全的設計、縱深防禦的概念以及如何管理產品生命週期,包含建立、維護以及產品失效的流程;二是在開發流程中,必須將產品開發的流程包含安全組態、更新管理政策以及其他相關的安全開發流程妥善的記錄並留存,同時也必須執行安全測試以達到IEC 62443-4-1的安全開發流程要求。
決定產品的安全強度-成熟等級(Maturity Level)與安全級別(Security Level)
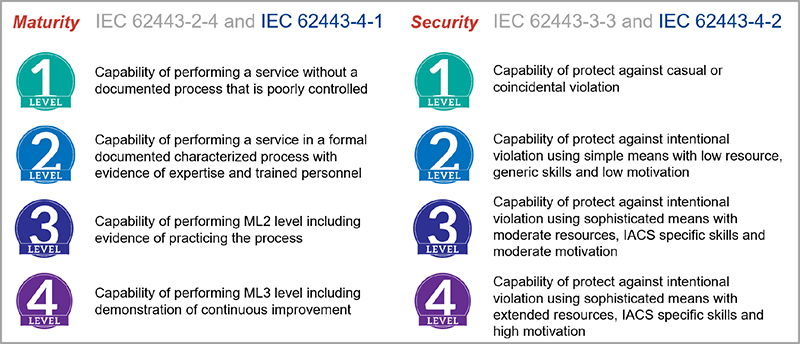
圖三:成熟等級(Maturity Level)與安全級別(Security Level)
每個機構對產品安全的因應程度有所不同,因此IEC62443除了定義出不同角色該遵循的流程外,也定義出流程成熟等級與產品安全級別(參考圖三:成熟等級(Maturity Level)與安全級別(Security Level)),讓想要取得認證的機構有更明確的參考基準。
IEC62443的成熟等級(Maturity Level),除了可做為機構評估內部現有開發流程成熟程度的參考外,也有利於讓機構選擇適當的成熟等級(Maturity Level)做為目標,對於要取得IEC62443-4-1認證的機構也有一個明確的指引方向。
除了成熟等級(Maturity Level)外,IEC62443也強調產品安全保證概念,因此在產品安全標準上也將產品安全級別(Security Level)分出了四個等級,每個等級要求的方向與要解決的攻擊類型都有不同要求,對於要取得IEC62443-4-2認證的機構,也需先設定要達到的產品安全級別(Security level)目標,才有依循的執行方向。
IEC62443的成熟等級(Maturity Level),除了可做為機構評估內部現有開發流程成熟程度的參考外,也有利於讓機構選擇適當的成熟等級(Maturity Level)做為目標,對於要取得IEC62443-4-1認證的機構也有一個明確的指引方向。
除了成熟等級(Maturity Level)外,IEC62443也強調產品安全保證概念,因此在產品安全標準上也將產品安全級別(Security Level)分出了四個等級,每個等級要求的方向與要解決的攻擊類型都有不同要求,對於要取得IEC62443-4-2認證的機構,也需先設定要達到的產品安全級別(Security level)目標,才有依循的執行方向。
IIoT工控資安解決方案
安華聯網已成功協助數十家廠商導入包含資訊安全管理系統(ISMS)、軟體安全開發流程(SSDLC)、GDPR(歐盟個人資料保護法)、FDA對資安要求、共同準則(ISO 15408)以及IEC 62443等;尤其是在2018年才公布的IEC 62443-4-1標準,安華聯網已協助多家廠商完成4-1標準導入,並已取得IEC 62443-4-1的證書。
此外在協助廠商導入過程中,我們發現IIOT設備開發商在開發安全流程上常見的問題包括:未管控軟體/靭體安全開發流程或需求、使用有已知弱點的套件管理、未建立安全事件回覆與追蹤機制等;安華聯網可針對企業常見之產品開發生命週期管理問題對症下藥,量身訂作合適的資安管理流程,同時也可提供連網設備安全解決方案-「HERCULES產品資安合規自動化平台」,輔以滿足合規要求。透過旗下「HERCULES SecFlow產品資安管理系統」,讓研發團隊在軟體設計與開發階段,就能透過開放原始碼風險管理(Open Source Risk Management)的方式,確認系統是否存在重大資安漏洞,從源頭加以防護與改正。同時可配合「HERCULES SecDevice弱點檢測自動化工具」,提供連網產品檢測環境配置與安全性評估等自動化功能,在超過120個測試項目中發掘已知和未知弱點,讓團隊可在設計與檢測階段雙管齊下,進行雙重安全把關,有效為產品項目在上市前,降低資安風險。
媒體報導
此外在協助廠商導入過程中,我們發現IIOT設備開發商在開發安全流程上常見的問題包括:未管控軟體/靭體安全開發流程或需求、使用有已知弱點的套件管理、未建立安全事件回覆與追蹤機制等;安華聯網可針對企業常見之產品開發生命週期管理問題對症下藥,量身訂作合適的資安管理流程,同時也可提供連網設備安全解決方案-「HERCULES產品資安合規自動化平台」,輔以滿足合規要求。透過旗下「HERCULES SecFlow產品資安管理系統」,讓研發團隊在軟體設計與開發階段,就能透過開放原始碼風險管理(Open Source Risk Management)的方式,確認系統是否存在重大資安漏洞,從源頭加以防護與改正。同時可配合「HERCULES SecDevice弱點檢測自動化工具」,提供連網產品檢測環境配置與安全性評估等自動化功能,在超過120個測試項目中發掘已知和未知弱點,讓團隊可在設計與檢測階段雙管齊下,進行雙重安全把關,有效為產品項目在上市前,降低資安風險。
媒體報導
参考資料:
[1] IEC/PAS 62443-3 Publicly available specification Pre-Standard
[2] IEC/PAS 62443-4-1 Secure Product Development Lifecycle Requirements