本網站使用cookies以改善您的使用體驗,並提供更優質的客製化內容。若您未改變cookies設定並繼續瀏覽我們的網站(點擊隱私權政策以獲得更多資訊),或點擊繼續瀏覽按鈕,代表您同意我們的隱私權政策及cookies的使用。
工控安全
21.Dec.2020
淺談智慧製造工廠的資安防禦實務(下)
輕忽工業控制系統的資訊安全,將造成重大的損失
上一篇我們談到在智慧工廠若做了錯誤的資安部署,將如何讓資安防護機制演變為資安缺口;這一篇我們將從偵測與監控機制看待工業資安風險。
由於工業生產的特性,產線製程具有一定的危險性;從原物料之輸入,自動化製程之各種切磋琢磨,所導致的物理與化學變化,到產品的產出,與剩餘廢棄物的處理等,只要其中任何環節,因為輕忽資訊安全,皆有可能影響到製程,進而造成重大的損失,包括:「人員健康、人身安全、環境保護問題、產線產出量的減少或停擺、產品良率減損、業務中斷、金融賠償、監管單位行政處罰、司法單位判刑、聲譽損失」等狀況,其中也包含許多企業所重視的「營業秘密、智慧財產權、商務合約中斷與賠償」等損失。
由於工業生產的特性,產線製程具有一定的危險性;從原物料之輸入,自動化製程之各種切磋琢磨,所導致的物理與化學變化,到產品的產出,與剩餘廢棄物的處理等,只要其中任何環節,因為輕忽資訊安全,皆有可能影響到製程,進而造成重大的損失,包括:「人員健康、人身安全、環境保護問題、產線產出量的減少或停擺、產品良率減損、業務中斷、金融賠償、監管單位行政處罰、司法單位判刑、聲譽損失」等狀況,其中也包含許多企業所重視的「營業秘密、智慧財產權、商務合約中斷與賠償」等損失。
智慧製造維運管理的第二道防線:持續偵測與監控(Continue Detection & Monitoring)
缺乏偵測與監控機制的影響
上一篇提到工廠的不良部署方式會增加被駭客攻擊的機率,若工廠又缺乏偵測與監控機制時,那麼當連網設備,例如:PLC,遭受阻斷服務攻擊導致產線停擺後,廠方第一線作業人員又缺乏資訊安全知識,極有可能會誤以為是PLC老化或當機,僅對PLC進行重新開機;又或許廠方有內聘的程式設計人員,便開始轉向要求寫控制程式的程式設計人員,修改PLC控制程式,以減少當機次數,然而缺乏偵測與監控機制的狀態下,一般的程式設計師也無法輕易瞭解問題發生原因,因此,真正問題發生的原因仍然無法被發現。
有效偵測與監控機制的重要性
根據OWASP[1]於2017年的統計,OWASP TOP 10列出的Web 10大資安風險,其中第10大風險,即為「不充分的日誌紀錄與監控」(Insufficient logging and monitoring),Web作為普遍的功能規格,同樣常見於工控系統中,因此,這類的資安風險不可輕視;而為數眾多的工控設備,其通訊所使用之規格是特定規格、或者是客製化的自訂通訊協定,皆有其獨特的設定模式,如此,不只難以進行弱點檢測,通常也因為設備的資料容量限制,而缺乏完整的監控與日誌紀錄,導致無法進行安全事件回覆與追蹤。因此,若偵測與監控的有效性不足,資安事件發生時也將無法做立即性的事件反應與處理,這就可能造成廠區停擺,而使企業產生經濟損失或相關危害。
攻擊場景示例:駭客是怎麼入侵的?
在攻擊之前:偵查(Reconnaissance)
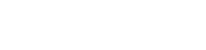
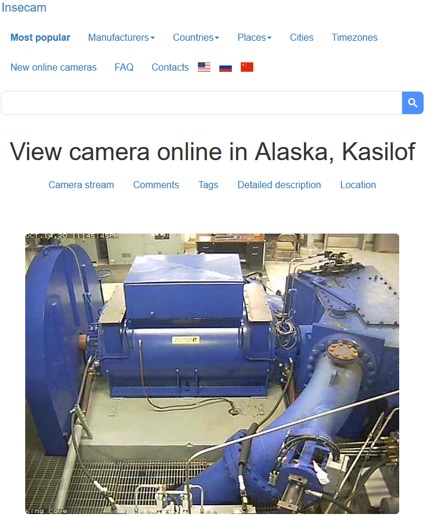
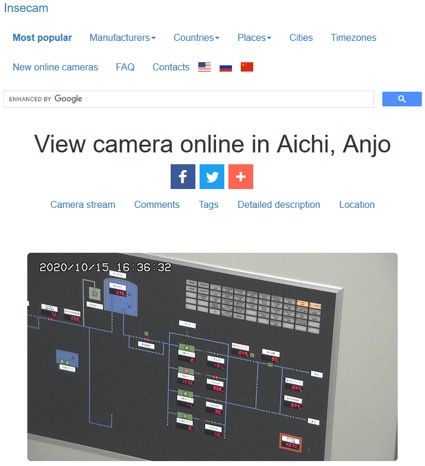
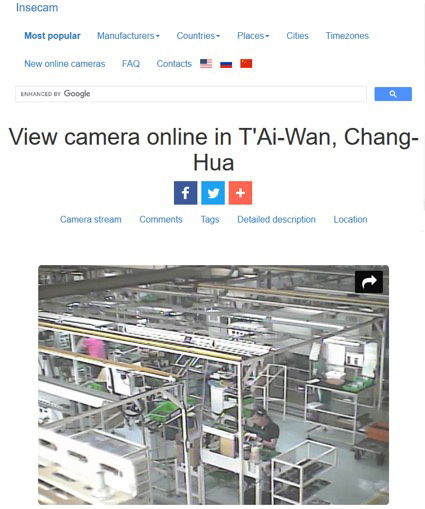
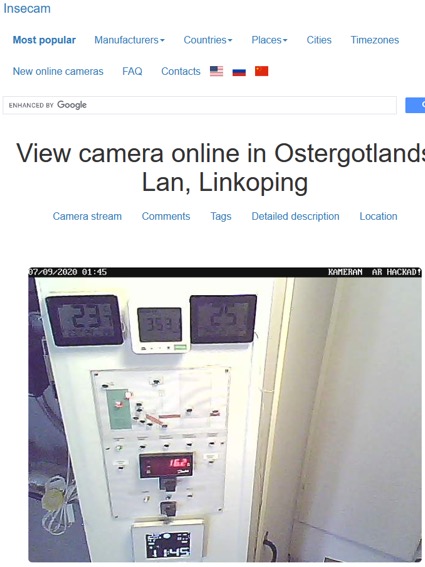
基於Shodan、Google與俄羅斯Yandex地圖的搜尋技術,同樣於資安領域知名的「insecam.org」[2]蒐羅全球的CCTV資料,內容有公開的地理位置、影片的說明也包含被公開CCTV的IPv4位址與通訊協定埠口。而其中大多數是交通與社區的公共監控影像,但仍有為數不少是不良部署而造成影像資料外洩的私人機構、家庭的CCTV影像以及廠區內作業影像等。insecam同時也包含 industrial、office等標籤,其中甚至還有能源、水利等八大關鍵基礎設施相關的影像。
透過遠端偵查,駭客獲得insecam的公開的地理位置後,得以鎖定目標廠區進行潛伏。
媒體報導
參考資料:
[1]《OWASP Top Ten》OWASP組織。閱於2020.Oct.15。網址:https://owasp.org/www-project-top-ten/
[2]《Insecam》Insecam組織。閱於2020.Jul.09~Oct.15。網址:https://www.insecam.org/en/
[3]《惡名昭彰的殭屍網路病毒Mirai作者之一被判賠償860萬美元》台灣iThome。閱於2020.Oct.16。網址:https://www.ithome.com.tw/news/126699
[4]《BASHLITE Malware Uses IoT for DDoS Attacks》Security Intelligence。閱於2020.Oct.16。網址:https://securityintelligence.com/news/bashlite-malware-uses-iot-for-ddos-attacks/
[5]《This new variant of Mirai botnet malware is targeting network-attached storage devices》ZDNet。閱於2020.Oct.16。網址:https://www.zdnet.com/article/this-new-variant-of-mirai-botnet-malware-is-targeting-network-attached-storage-devices/
[6]《Grandstream and DrayTek Devices Exploited to Power New Hoaxcalls DDoS Botnet》Palo Alto Networks之IoC報告。閱於2020.Oct.16。網址:https://unit42.paloaltonetworks.com/new-hoaxcalls-ddos-botnet/
[7]《什麼是 APT進階持續性威脅 (Advanced Persistent Threat, APT)?》Trend Micro。閱於2020.Oct.16。網址:https://blog.trendmicro.com.tw/?p=123
[8]《Most ICS vulnerabilities disclosed this year can be exploited remotely》Help Net Security。閱於2020.Oct.16。網址:https://www.helpnetsecurity.com/2020/08/20/ics-vulnerabilities-exploited-remotely/
[9]《MITRE ATT&CK MATRIX》MITRE組織。閱於2020.Jul.08。網址:https://attack.mitre.org/
[10]《Building Trojan Hardware at Home》BlackHat 2014。閱於2020.Jul.09。網址:https://www.blackhat.com/docs/asia-14/materials/Dunning/Asia-14-Dunning-Building-Trojan-Hardware-At-Home.pdf
[11]《The 'killer USB' that FRIES laptops: Malicious drive uses a high voltage to destroy the computer's circuit board》Daily Mail。閱於2020.Oct.15。網址:https://www.dailymail.co.uk/sciencetech/article-2997401/The-killer-USB-FRIES-laptops-Malicious-drive-uses-high-voltage-destroy-computer-s-circuit-board.html
[12]《Knowing Your Employees - An Overview》Management Study Guide。閱於2020.Oct.16。網址:https://www.managementstudyguide.com/knowing-your-employees.htm
[13]《世界備份日( World Backup Day):三二一原則》Trend Micro。閱於2020.Oct.16。網址:https://blog.trendmicro.com.tw/?p=4707
[14]《What is Cyber Hygiene? A Definition of Cyber Hygiene, Benefits, Best Practices, and More》Digital Guardian。閱於2020.Oct.16。網址:https://digitalguardian.com/blog/what-cyber-hygiene-definition-cyber-hygiene-benefits-best-practices-and-more
 |
 |
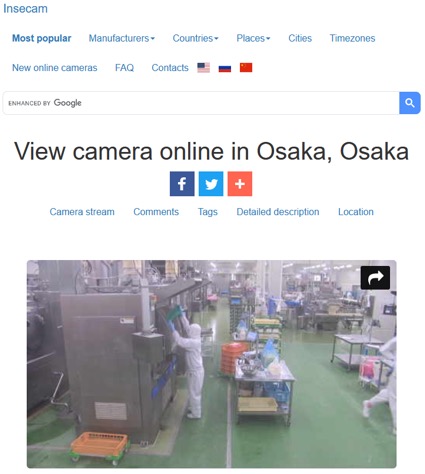 |
| 美國阿拉斯加水力發電廠外洩影像 | 日本愛知水利設施外洩的影像 | 日本大阪某食品加工廠外洩的內部作業影像 |
 |
 |
 |
| 彰化某工廠的影像外洩 | 台北新光華商場以北附近, 松江路上的小巷弄,某私人設備進行3D列印的影像外洩 |
瑞典某處的CCTV已遭駭客入侵(Jul.09.2020) |
透過遠端偵查,駭客獲得insecam的公開的地理位置後,得以鎖定目標廠區進行潛伏。
攻擊方法一:透過遠端連線利用裝置已知的弱點入侵目標
2016年惡名昭彰的惡意軟體「Mirai」[3]感染網際網路上諸多的CCTV等裝置,以及許多物聯網設備遭到惡意軟體「BASHLITE」[4]入侵感染,只因軟體研發時採用「含有弱點的BusyBox」套件,且無法進行軟體更新,這兩種知名的惡意軟體,都是感染裝置後,將裝置作為殭屍網路,發動多次造成企業嚴重損失的「分散式阻斷服務攻擊(DDoS)」,並且目前仍有不少改造的變種[5][6]持續於網際網路上進行攻擊與感染。除了DDoS之外,目前常見還有勒索軟體的侵擾,甚至是所謂的「進階持續性滲透攻擊」(Advanced Persistent Threat, APT)[7]等。根據統計,工控系統(ICS)已知弱點中70%可被遠端利用,而其中以利用遠端代碼執行的弱點,駭進工控系統的比率占了49%,駭入之後進行DoS攻擊的比率也可高達39%。[8]攻擊方法二:進行供應鏈滲透進行實體入侵,導致不安全的供應鏈
根據MITRE ATT&CK矩陣[9]所提及不安全的供應鏈(Supply Chain Compromise),在工控領域中比較有可能發生的情況,包含:駭客有可能會從軟體更新機制下手,進行軟體置換、攔截零組件或設備,加以植入惡意程式、偽冒成上下游與協力廠商的供應商,向各廠商兜售有問題的零組件等;也有可能如同先前某知名積體電路公司的勒索病毒事件,由協力廠商無意間攜入附有惡意軟體的設備,造成廠區內的設備破壞。現代製造業的經濟模式,必然有上游廠商、協力廠商、與下游廠商,因此,應該要注重並加強資安的管理。攻擊方法三:利用缺乏辨識資產設備的機制進行實體入侵
MITRE ATT&CK矩陣[9]也有提及「硬體增加」(Hardware Additions)一事,指駭客有可能就挾帶惡意硬體進入廠區,未經檢查與授權的硬體增加,可能導致硬體功能性的改變、資訊外洩、降低硬體可信度、阻斷服務等結果。例如:微型攝影設備、內含惡意程式的外接磁碟機、微型的無線訊號收集與發送器、在網路線的其中一端插入訊息側錄機;使用內含高壓電之電容的USB或乙太網路線,毀損設備以阻斷生產等手法。如何避免被增減軟硬體這類的實體入侵,加強資產的盤點與辨識及資料流的監控,將是爾後重要的議題。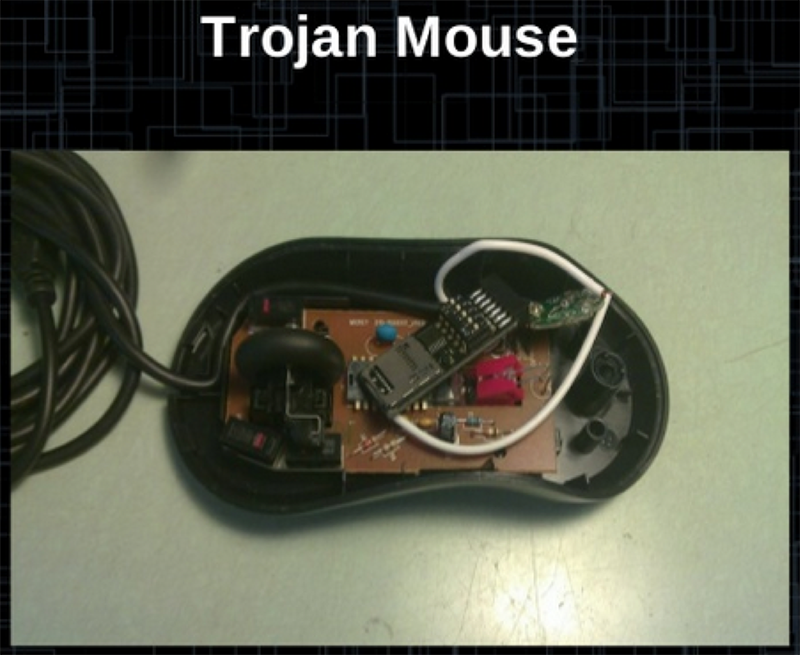 |
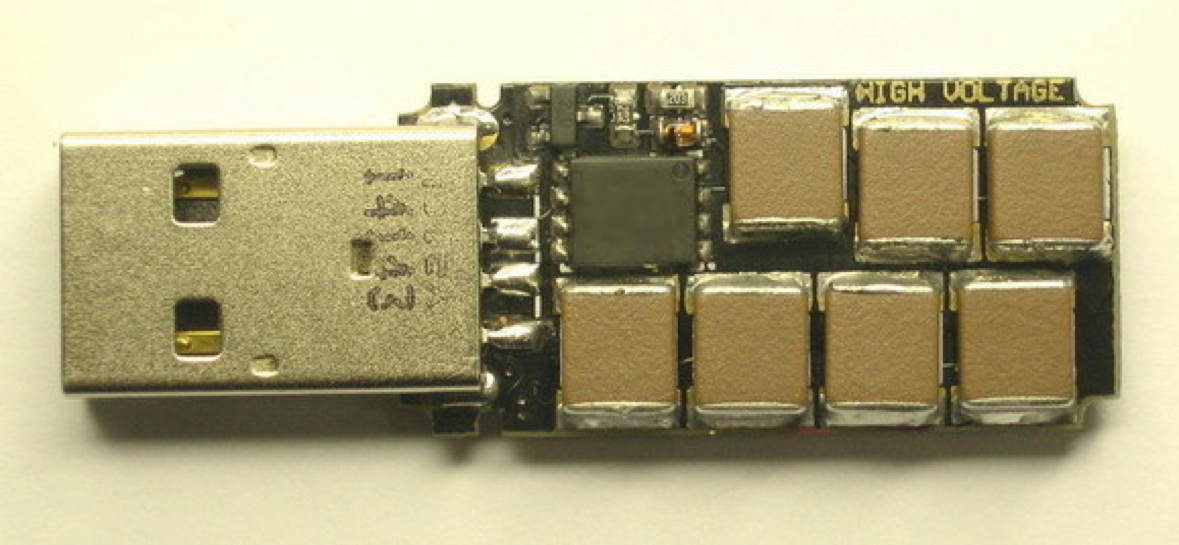 |
| 國際黑帽2014亞洲區大會,講者展示被增加惡意硬體的滑鼠[10] | 2015年俄羅斯駭客研發USB Killer,接上裝置能釋出高壓電,損毀沒有電壓保護的硬體[11] |
防禦實務:進行安全管理(Security Management)
1. 建立安全管理計畫(Plan)
- 企業高層進行「安全性承諾」,初始化安全管理。
- 建立合規的維運監控計畫,以下為可參考標準:IEC-62443系列、IEC-61511系列、IEC/ISO-27000系列、IES/ISO-27036、NIST SP 800-82、 NIST SP 800-39等系列的資訊安全標準。
- 根據所導入的標準,建立「資訊安全管理」程序書與查檢表,包含「風險評估」等流程。
- 所採購的硬體設備與軟體,需要「應有且有效」的「資安監控」與「安全流程管理」;或可選擇已經由第三方認證認可的軟硬體,例如採用通過ISO/IEC 15408:安全評估共通準則(Common Criteria)的產品。
- 加強對員工的瞭解(KYE: Know Your Employees)[19]。
- 面對「最糟狀況」的可能性,要有應對的計畫。
- 百密仍可能有一疏,投保資安保險,以應對資安事件造成的經濟損失。
2. 執行安全管理程計畫(Do)
- 盤點與分類各種軟體、硬體資產。
- 依照所導入的資安標準之各項「控制措施」,實作資安要求。
- 定期以「3-2-1備份原則」[13]進行資料備份,並預留備用硬體設備,以預防天災、人為疏失、惡意軟體破壞。
- 必須假設已經被駭客入侵,進行資產的「資安與網路衛生」(Cyber Hygiene) [14]檢查。
- 調整作業系統的安全原則,以符合所導入的資安標準要求。
- 設定內部聯網許可名單(Allowed List),必要時啟用IPsec或MACsec設定。
- 強化內部網路安全偵測,持續維持「網路衛生」。
- 進行每個存取點之間,資料流(Data Flow)的紀錄與分析。
- 應對資安事件發生,對事件採取「零信任」(Zero Trust)。
- 要有監看軟體日誌之充足人力配置。
- 定期養護硬體設備。
- 要求軟體安全更新來自可信任的來源,甚至具有簽章效力。
3. 定期進行內部與外部稽核(Check)
- 加強內部資安管理與稽核人員之教育訓練。
- 定期進行資產使用年限評估。
- 定期檢查硬體設備與軟體日誌。
- 依照所導入的資安標準,所建立的查檢表,逐一稽核。
- 將稽核結果進行文件化。
- 依照法規回報資安事件與應變措施。
4. 檢討、改善安全缺失並修訂安全管理程計畫(Act.)
- 依照資安事件與標準,比較未緩解的安全缺失與可容忍的安全缺失。
- 辨識與評估現有的應變措施。
- 重新評估資安事件再度發生的可能性與衝擊。
- 辨識額外資安應變措施。
- 將額外應變措施加入安全管理計畫。
安華聯網所提供的智慧製造工廠資安解決方案
安華聯網的智慧製造工廠資安解決方案,包含ISO 27001與IEC 62443合規服務、針對工控產品或系統軟、硬體的資安檢測服務(包含PLC、ICS、SCADA等智慧製造相關之工控元件)、以及自主研發的產品資安合規自動化平台-HERCULES,可針對智慧製造工廠資安常見的安全弱點進行掃描與管理。此外,安華聯網更提供軟體安全開發指導服務,協助廠商具備軟體安全開發能量,進行專業的軟體開發安全教育訓練、維運資訊安全管理教育訓練,幫助技術人員建立與工業物聯網相關的資安意識,以因應未來智慧製造的建置以及工業4.0時代的來臨。媒體報導
參考資料:
[1]《OWASP Top Ten》OWASP組織。閱於2020.Oct.15。網址:https://owasp.org/www-project-top-ten/
[2]《Insecam》Insecam組織。閱於2020.Jul.09~Oct.15。網址:https://www.insecam.org/en/
[3]《惡名昭彰的殭屍網路病毒Mirai作者之一被判賠償860萬美元》台灣iThome。閱於2020.Oct.16。網址:https://www.ithome.com.tw/news/126699
[4]《BASHLITE Malware Uses IoT for DDoS Attacks》Security Intelligence。閱於2020.Oct.16。網址:https://securityintelligence.com/news/bashlite-malware-uses-iot-for-ddos-attacks/
[5]《This new variant of Mirai botnet malware is targeting network-attached storage devices》ZDNet。閱於2020.Oct.16。網址:https://www.zdnet.com/article/this-new-variant-of-mirai-botnet-malware-is-targeting-network-attached-storage-devices/
[6]《Grandstream and DrayTek Devices Exploited to Power New Hoaxcalls DDoS Botnet》Palo Alto Networks之IoC報告。閱於2020.Oct.16。網址:https://unit42.paloaltonetworks.com/new-hoaxcalls-ddos-botnet/
[7]《什麼是 APT進階持續性威脅 (Advanced Persistent Threat, APT)?》Trend Micro。閱於2020.Oct.16。網址:https://blog.trendmicro.com.tw/?p=123
[8]《Most ICS vulnerabilities disclosed this year can be exploited remotely》Help Net Security。閱於2020.Oct.16。網址:https://www.helpnetsecurity.com/2020/08/20/ics-vulnerabilities-exploited-remotely/
[9]《MITRE ATT&CK MATRIX》MITRE組織。閱於2020.Jul.08。網址:https://attack.mitre.org/
[10]《Building Trojan Hardware at Home》BlackHat 2014。閱於2020.Jul.09。網址:https://www.blackhat.com/docs/asia-14/materials/Dunning/Asia-14-Dunning-Building-Trojan-Hardware-At-Home.pdf
[11]《The 'killer USB' that FRIES laptops: Malicious drive uses a high voltage to destroy the computer's circuit board》Daily Mail。閱於2020.Oct.15。網址:https://www.dailymail.co.uk/sciencetech/article-2997401/The-killer-USB-FRIES-laptops-Malicious-drive-uses-high-voltage-destroy-computer-s-circuit-board.html
[12]《Knowing Your Employees - An Overview》Management Study Guide。閱於2020.Oct.16。網址:https://www.managementstudyguide.com/knowing-your-employees.htm
[13]《世界備份日( World Backup Day):三二一原則》Trend Micro。閱於2020.Oct.16。網址:https://blog.trendmicro.com.tw/?p=4707
[14]《What is Cyber Hygiene? A Definition of Cyber Hygiene, Benefits, Best Practices, and More》Digital Guardian。閱於2020.Oct.16。網址:https://digitalguardian.com/blog/what-cyber-hygiene-definition-cyber-hygiene-benefits-best-practices-and-more