本網站使用cookies以改善您的使用體驗,並提供更優質的客製化內容。若您未改變cookies設定並繼續瀏覽我們的網站(點擊隱私權政策以獲得更多資訊),或點擊繼續瀏覽按鈕,代表您同意我們的隱私權政策及cookies的使用。
資安事件
11.Jan.2021
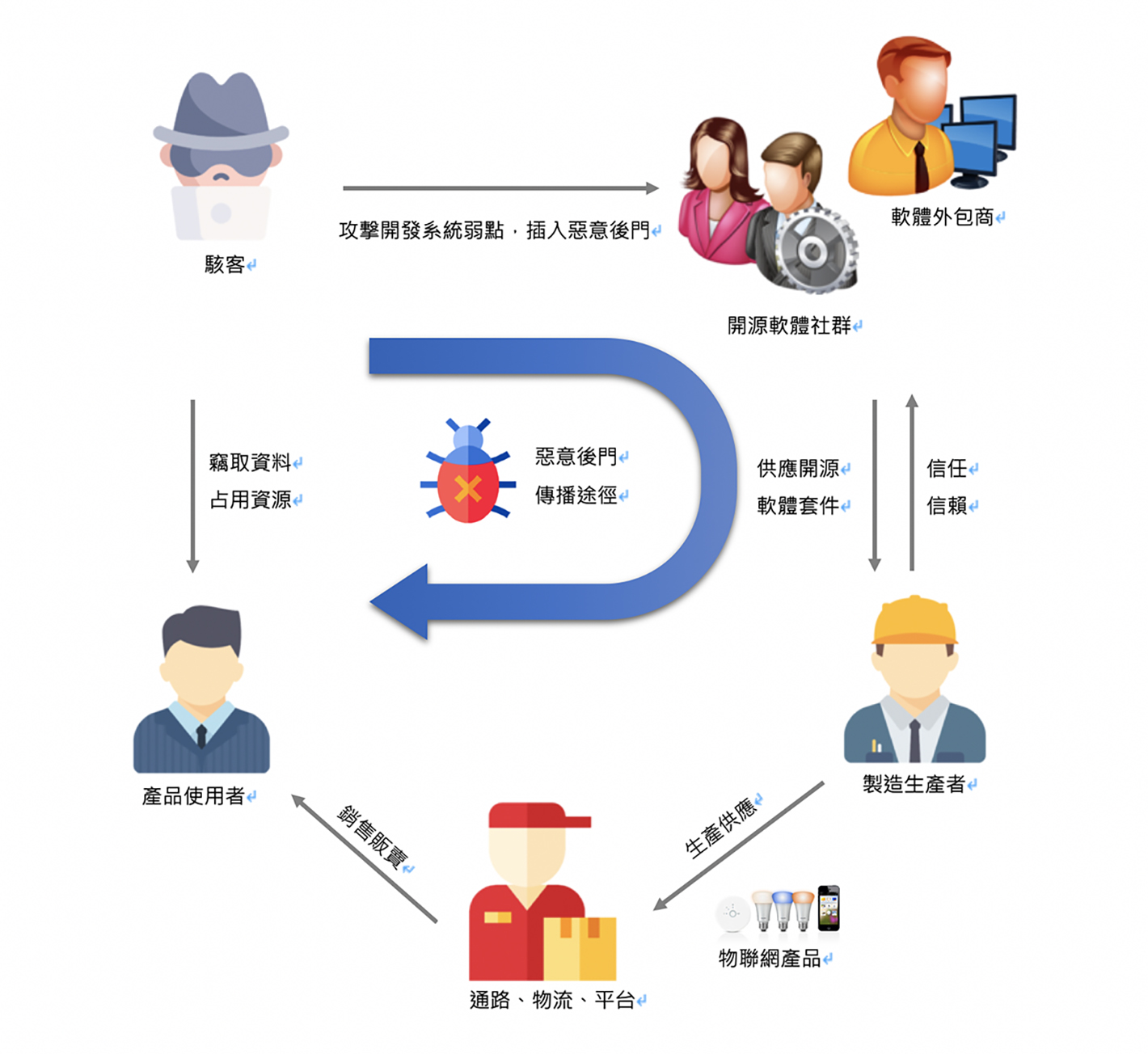
惡意駭客利用開源軟體進行供應鏈攻擊 開源社群成為代罪羊
駭客攻擊手法與入侵型態日趨多元,在企業網路橫行多年的APT攻擊也逐步將場域轉移至供應鏈安全上,其中又以開源軟體安全問題最容易被資安團隊忽略,所以更受駭客青睞。著名的開源碼專案GitHub便曾被駭客鎖定,直接將惡意程式植入開源專案中,讓所有引用開源碼的開發人員無意間成了為駭客建立後門程式的幫手,這些含有後門程式的產品上市後,便會散布在家用網路、企業網路、關鍵基礎設施等,直接讓駭客擴大攻擊場域。對產品製造商而言,隨之而來的就是修補弱點工作,甚至會有金錢與商譽的損失。
其實上述的狀況只要可以在產品上市前,將資安意識提前至開發過程中執行便可以避免;其中一個最經濟實惠的方式,是在開發期間,藉由自動化工具找出第三方開放源始碼套件弱點,管理並修補發現的弱點,才能避免成為供應鏈中的安全破口,降低弱點被利用的風險。
其實上述的狀況只要可以在產品上市前,將資安意識提前至開發過程中執行便可以避免;其中一個最經濟實惠的方式,是在開發期間,藉由自動化工具找出第三方開放源始碼套件弱點,管理並修補發現的弱點,才能避免成為供應鏈中的安全破口,降低弱點被利用的風險。
安華聯網解決方案
開源碼弱點檢測:【HERCULES SecSAM】讓研發團隊在軟體設計與開發階段,檢查所使用的第三方開放源始碼套件是否存在爭議性授權問題及重大資安弱點;【HERCULES SecDevice】,可供連網產品檢測環境配置與安全性評估等自動化功能,提供超過140個安全測試項目,可協助在開發過程中發掘IoT產品對可能造成緩衝區益位、越界寫入等未知弱點及已知弱點進行挖掘,讓產品問題從源頭加以改正。
資安合規與認驗證服務:可針對企業常見之產品開發生命週期管理問題對症下藥,量身訂作合適的資安管理流程,同時提供廠商資安稽核服務、資安改善暨合規符合性檢視服務,可協助廠商快速取得產品國際資安證書。
參考資料:
https://www.ithome.com.tw/news/137953 https://www.nccst.nat.gov.tw/NewsRSSDetail?lang=zh&RSSType=news&seq=16401
https://www.mdeditor.tw/pl/29Sr/zh-tw https://www.securityweek.com/backdoor-found-rest-client-ruby-gem
https://github.com/rest-client/rest-client/issues/713 https://nvd.nist.gov/vuln/detail/CVE-2019-15224
https://www.zdnet.com/article/backdoor-found-in-webmin-a-popular-web-based-utility-for-managing-unix-servers/
https://nvd.nist.gov/vuln/detail/CVE-2019-15107 https://www.nccst.nat.gov.tw/NewsRSSDetail?lang=zh&RSSType=news&seq=16401
資安合規與認驗證服務:可針對企業常見之產品開發生命週期管理問題對症下藥,量身訂作合適的資安管理流程,同時提供廠商資安稽核服務、資安改善暨合規符合性檢視服務,可協助廠商快速取得產品國際資安證書。
參考資料:
https://www.ithome.com.tw/news/137953 https://www.nccst.nat.gov.tw/NewsRSSDetail?lang=zh&RSSType=news&seq=16401
https://www.mdeditor.tw/pl/29Sr/zh-tw https://www.securityweek.com/backdoor-found-rest-client-ruby-gem
https://github.com/rest-client/rest-client/issues/713 https://nvd.nist.gov/vuln/detail/CVE-2019-15224
https://www.zdnet.com/article/backdoor-found-in-webmin-a-popular-web-based-utility-for-managing-unix-servers/
https://nvd.nist.gov/vuln/detail/CVE-2019-15107 https://www.nccst.nat.gov.tw/NewsRSSDetail?lang=zh&RSSType=news&seq=16401