本網站使用cookies以改善您的使用體驗,並提供更優質的客製化內容。若您未改變cookies設定並繼續瀏覽我們的網站(點擊隱私權政策以獲得更多資訊),或點擊繼續瀏覽按鈕,代表您同意我們的隱私權政策及cookies的使用。
資安事件
22.Mar.2022
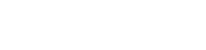
DDoS攻擊再進化:封包能放大 65 倍的TCP Middlebox Reflection
最近幾週,國外研究人員觀察到多次分散式阻斷服務 (Distributed Denial of Service, DDoS) 攻擊活動,其中包括 SYN 洪水(SYN Flooding)攻擊等大流量攻擊,最高流量可達 11 Gbps。研究人員在分析這幾次DDoS攻擊中使用的封包之後,發現駭客正在使用一種稱為 TCP Middlebox Reflection的新技術[1]。這是一種非常新的攻擊手法,於 2021 年 8 月在馬里蘭大學和科羅拉多大學博爾德分校的研究人員撰寫的一篇論文中首次被提出[2],駭客可以輕鬆的將攻擊封包流量放大 65 倍,這將對網路設備構成嚴重威脅[3]。
認識新型態DDoS攻擊技術:TCP Middlebox Reflection
以往DDoS攻擊大多搭配放大攻擊(Amplification Attack)技術,讓駭客可以產生比原本所發出的封包數倍、甚至是數十倍大的封包流量進行攻擊。目前常見用於執行放大攻擊包括網域名稱系統(DNS)、簡易網路管理通訊協定(SNMP)、網路時間協定(NTP)及通用隨插即用協定(UPnP)等基於UDP通訊的通訊協定,利用UDP通訊協定的特性,攻擊者可將來源IP位址偽冒成受害主機,攻擊主機只要發送一個簡單的查詢封包給伺服器(Server),之後伺服器便會將大量的資料內容回傳給受害主機。攻擊者便可利用放大攻擊手法,同時讓數十萬台甚至數百萬台的主機同時發出查詢封包,即可發動一次具有相當規模的DDoS攻擊。
以往攻擊者大多使用UDP-Based Reflection方式作攻擊,因為UDP通訊協定無需和伺服器建立連線即可進行資料傳輸,而TCP通訊協定則是需要先跟伺服器進行TCP三方交握(TCP 3-way Handshake),且因TCP三方交握的特性,使得攻擊者無法在偽造來源IP位址的情況下與伺服器完成TCP三方交握。TCP Middleboxes Reflection攻擊技術的出現,利用防火牆、入侵防禦/偵測系統及網頁內容過濾產品等具備封包內容檢查功能的網路裝置,具備較好的封包容錯能力,對於未依據TCP協定方式傳送的封包內容仍然會允許接受與轉送至目的IP位址,攻擊者即可利用此特性使用TCP連線發起反射式放大攻擊。
以往攻擊者大多使用UDP-Based Reflection方式作攻擊,因為UDP通訊協定無需和伺服器建立連線即可進行資料傳輸,而TCP通訊協定則是需要先跟伺服器進行TCP三方交握(TCP 3-way Handshake),且因TCP三方交握的特性,使得攻擊者無法在偽造來源IP位址的情況下與伺服器完成TCP三方交握。TCP Middleboxes Reflection攻擊技術的出現,利用防火牆、入侵防禦/偵測系統及網頁內容過濾產品等具備封包內容檢查功能的網路裝置,具備較好的封包容錯能力,對於未依據TCP協定方式傳送的封包內容仍然會允許接受與轉送至目的IP位址,攻擊者即可利用此特性使用TCP連線發起反射式放大攻擊。
新型態DDoS攻擊技術大幅降低攻擊門檻
Akamai 安全情報研究團隊負責人 Chad Seaman 指出, TCP Middlebox Reflection攻擊的規模正逐漸成長。使用此技術的第一波攻擊活動可能始於 2 月中旬。這些攻擊襲擊了包含網路託管、媒體、旅遊、銀行和遊戲服務的網站伺服器。雖然目前為止觀察到利用此技術的攻擊相對較少,但利用規模確實在持續增長中,安全研究團隊預測攻擊者將會進一步嘗試改進和擴大攻擊。
隨著這項新的攻擊手法增加了執行 DDoS攻擊手法的變化,企業應依據各種攻擊途徑與手法,檢視自身的安全防禦策略,以更彈性、更完備的準備因應挑戰。
隨著這項新的攻擊手法增加了執行 DDoS攻擊手法的變化,企業應依據各種攻擊途徑與手法,檢視自身的安全防禦策略,以更彈性、更完備的準備因應挑戰。
DDoS演練服務,快速建立或驗證應變機制
安華聯網透過自主研發的分散式阻斷服務 (DDoS) 攻擊平台提供演練服務,模擬來自國內外的DDoS攻擊。該平台整合多個國際知名雲端基礎架構服務業者,最高可模擬2,000個不同來源IP位址,進行400G位元組網路流量或100萬個應用程式連線的DDoS演練服務,客戶可依其需求自行定義演練過程所需要的流量、連線數、IP數及執行時間,並能設計多個演練情境在指定時間自動執行,以驗證網站或應用程式等目標系統與DDoS防禦機制的可用性與有效性。透過DDoS演練服務,企業可從過程中發現,在不同階段目標系統的反應狀況,演練結束後可以參考演練過程所設計的情境,作為企業後續規劃系統架構效能調校,及擬定DDoS緩解與應變措施的依據。
參考資料:
[1] https://www.akamai.com/blog/security/tcp-middlebox-reflection
[2] https://www.usenix.org/system/files/sec21fall-bock.pdf
[3] https://thehackernews.com/2022/03/hackers-begin-weaponizing-tcp-middlebox.html