White Papers
Onward Security analyzes the SBOM management countermeasures to resolve the cybersecurity breaches in the software supply chain step by step
As the epidemic accelerates digital transformation, cybersecurity threats continue to intensify. As a result, many countries or industries have introduced more stringent cybersecurity regulations, requiring manufacturers of networking equipment to establish a Software Bill of Materials (SBOM) as a basis to strengthen the security of the software supply chain.
Tso Jen Liu, Chief Technology Officer of Onward Security, said that it is impossible to rely on a single operation (such as testing) to ensure product security. Instead, it is necessary to inject a culture of cybersecurity into the organization, and achieve the goal through continuous operation and improvement.
It is worth mentioning that the United States, Canada, Europe, and even the Asia-Pacific region (such as Japan, South Korea, Singapore and Taiwan) have now issued regulations on software supply chain security. For example, Taiwan Ministry of Health and Welfare issued the "Guidance for Industry on Management of Cybersecurity in Medical Devices" in May 2021, which clearly requires manufacturers to provide SBOM as pre-market review information.
IoT Security Trend: Easily Addressing Open Source Software Security Blind Spots with Firmware Scanning.
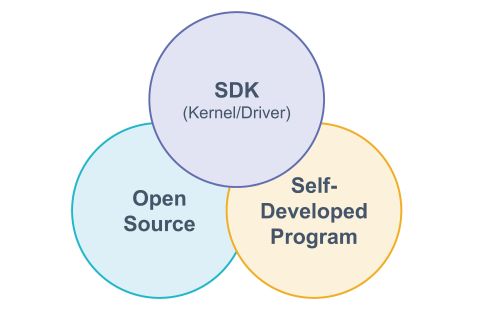
After more than a decade of development, the application of open-source software has reached a mature stage. Starting from 2008, Gartner has released multiple research reports indicating that the proportion of open-source software in "business applications," "cloud computing services," and "information infrastructure" will continue to increase.
How to solve unknown cybersecurity vulnerabilities and threats? Understanding the fuzz testing
In the past, hackers used to attack known vulnerabilities to achieve the purpose of intrusion, but now more and more attackers are gradually starting to use unknown vulnerabilities to launch zero-day attacks and their methods are gradually becoming mature. Attacking the defenseless IoT devices with malicious programs targeting unknown vulnerabilities has become the favorite of attackers.