Services
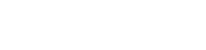
Cybersecurity Diagnostics Assessment
Providing comprehensive cybersecurity testing services for networks, systems, and personnel, so as to strengthen the information security management system, solve cybersecurity protection problems, prevent potential threats and attacks, and ensure overall enterprise security.
Assessment Item
-
 System Security
System SecurityWebsite and System Security Testing
Websites, hosts, connected devices, and more are proceeded with vulnerability tests to scan if there are any CVE or security issues caused by improper settings. -
 System Security
System SecurityMalware Detection
Detect personal computers and servers that Whether there is malware existing.
-
 System Security
System SecuritySystem Settings and Update Checks
Based on the security configuration benchmark published by the government, it is to ensure organizations' implementation.
-
 Network Security
Network SecurityNetwork Architecture Check
Utilize the network architecture diagram to present the Status, network appliance, and servers' locations, areas, and IP configuration for system administrators' future management. -
 Network Security
Network SecurityMalicious Activity Detection
Through network data packet monitoring and network equipment log analysis to understand the organization, and whether the network has abnormal connection status. -
 Personnel Security
Personnel SecurityEmail Social Engineering
Simulate hacking phishing emails to detect employees' cybersecurity risk awareness, and analyze their behaviors, as well as provide training to reduce security risks caused by human error.
Features
-
 Cybersecurity diagnostics assessment covers three aspects including network security, system security, and personnel security protection.
Cybersecurity diagnostics assessment covers three aspects including network security, system security, and personnel security protection. -
 Combining automated tools and manual analysis operations, it provides professional cybersecurity diagnosis reports and correction suggestions.
Combining automated tools and manual analysis operations, it provides professional cybersecurity diagnosis reports and correction suggestions.
-
 With in-depth detection technology and professional consultant team, Onward Security has been dedicated to cybersecurity in government, finance, IIoT, IoT, and other industries.
With in-depth detection technology and professional consultant team, Onward Security has been dedicated to cybersecurity in government, finance, IIoT, IoT, and other industries. -
 Flexible cybersecurity diagnosis services provide customized solutions according to the current situation and customers' needs.
Flexible cybersecurity diagnosis services provide customized solutions according to the current situation and customers' needs.
Other Service
-
Red Team
The red team assessment not only focuses on the security-resistant protection of a single system but also emphasizes the protection breadth of the enterprise boundary network....... -
DDoS Simulation
In recent years, attackers have often used distributed denial-of-service (DDoS) attacks to try to paralyze the target website, causing users to be unable to connect to the website......